Inside the Release — Five Categories, Separation, and the Technical Rulings
The five categories, the separation doctrine that lets tokens stop being securities, and every technical ruling — mining, staking, wrapping, airdrops — in one place.
The previous post established the lens: the Howey test, the elimination method, the 2×2 matrix, and the reason "efforts of others" is the decisive prong. This post walks through what Release 33-11412 actually does with that lens — the five categories it creates, the separation concept it introduces, and the technical rulings it delivers on mining, staking, wrapping, and airdrops.
1. The five categories (§III, pp. 13–24)
Release 33-11412 sorts every crypto asset into one of five buckets. The sorting criterion is always the same: where does the asset sit relative to the essential-managerial-efforts line?
A useful way to read this taxonomy: it is not really five parallel categories. It is four safe harbors — Commodities, Collectibles, Tools, Stablecoins — plus one residual category (Digital Securities) that catches everything else. Each safe harbor represents a zone on the essential-managerial-efforts spectrum where the Commission has determined that the "efforts of others" prong is not met. A crypto asset that falls within any of the four harbors is outside the securities perimeter; a crypto asset that fails to reach any harbor defaults into the residual. This matters for securities analysis because the practical question is never "which of the five categories does this token belong to?" — it is "does this token qualify for any of the four safe harbors, and if not, it is a security."
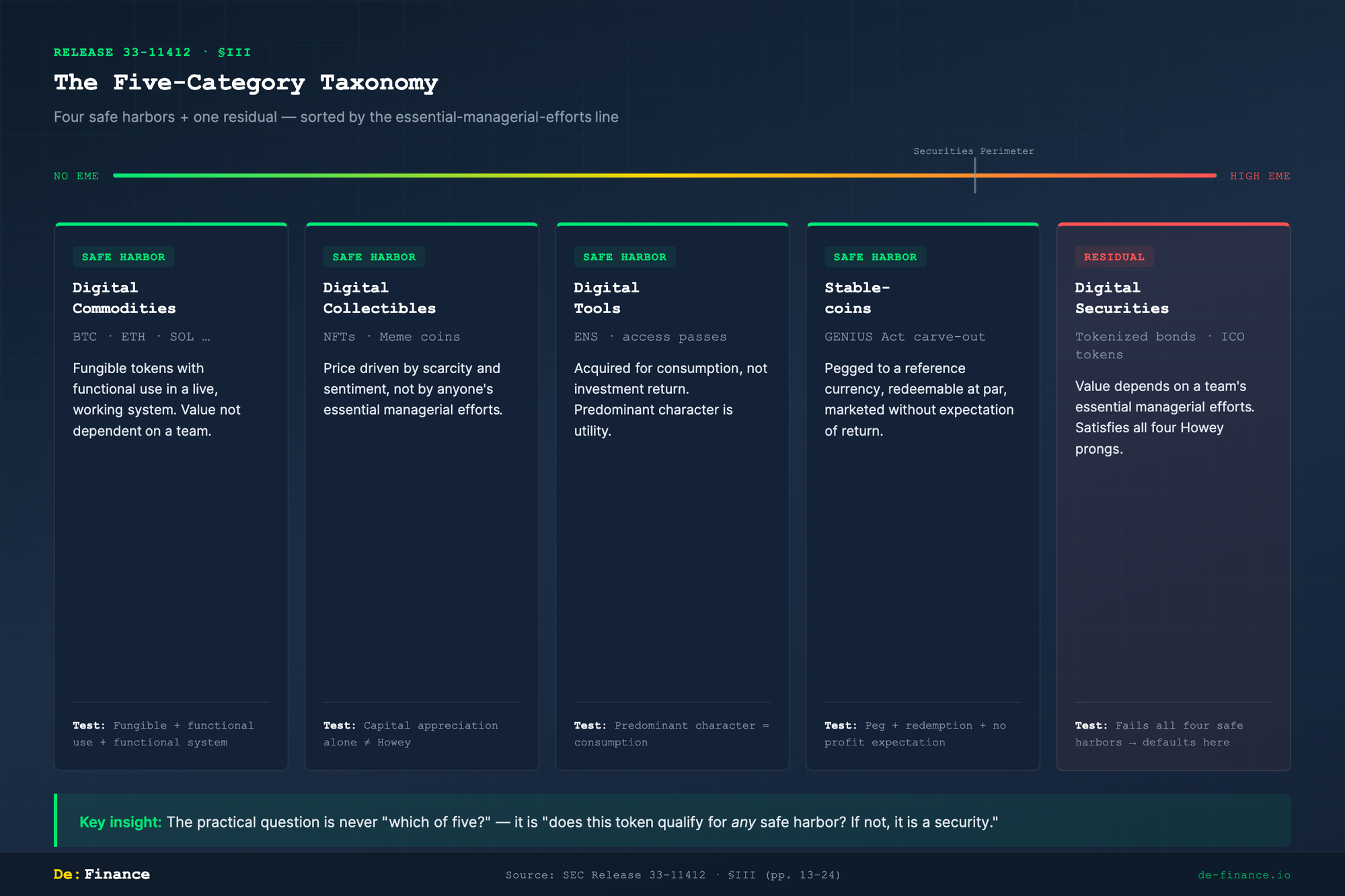
1-A. Digital Commodities (§III.A, pp. 14–16)
The release names approximately twenty tokens — including BTC, ETH, and SOL — as digital commodities. Three criteria must be met:
| Criterion | What it means |
|---|---|
| Fungible | One unit is interchangeable with another |
| Functional use | The token does something inside a system (transfers value, pays fees, secures a network) |
| Functional system | The system in which it operates is live and working |
The crucial negative condition: the token's value is not primarily dependent on the essential managerial efforts of an identifiable team.
Two things to note. First, the list is illustrative, not exhaustive. Other tokens can qualify if they meet the same criteria. Second, a digital commodity can be sold as part of an investment contract — for instance, in an ICO where the promoter promises to build a network. In that case the transaction is a securities offering, but the asset itself remains a commodity. When the investment-contract wrapper falls away (see Section 2 below), the token trades as a commodity in the secondary market.
1-B. Digital Collectibles (§III.B, pp. 16–20)
NFTs and meme coins land here. The core reasoning: capital appreciation alone does not satisfy Howey. A buyer may hope a rare NFT or a meme coin will go up in price, but if that price is driven by scarcity, cultural sentiment, or speculative demand rather than by anyone's essential managerial efforts, the "efforts of others" prong is not met.
This is the release's most contested classification. Critics argue that many NFT projects have centralized teams whose roadmap decisions drive floor prices — pushing those projects back toward the securities side. The release acknowledges this: the analysis is always fact-specific. An NFT tied to a revenue-sharing promise from a studio could be a security, even if a standalone JPEG is not.
1-C. Digital Tools (§III.C, pp. 20–21)
Tokens acquired primarily for consumption — domain names, access passes, in-protocol utility — rather than for investment return. The release points to ENS as a prototype.
The key test is predominant character. If a token is marketed overwhelmingly as a way to earn yield or appreciate in value, the "digital tool" label does not apply regardless of what utility features exist. The inquiry looks at the asset's primary economic reality, not the label its creator gave it.
1-D. Stablecoins (§III.D, pp. 21–23)
The GENIUS Act (signed July 2025) carved out "payment stablecoins" from the statutory definition of a security. The release incorporates that carve-out. A qualifying stablecoin must meet three conditions:
| Condition | Requirement |
|---|---|
| Peg | Fixed to a reference currency (typically USD) |
| Redemption | Redeemable at par on demand |
| No profit expectation | Marketed without expectation of return |
If a stablecoin's issuer advertises yield or investment return, the carve-out does not apply and the token may be analyzed as a security.
1-E. Digital Securities (§III.E, pp. 23–24)
The residual category. Two sub-types:
Tokenized securities — traditional financial instruments (bonds, equity, fund interests) issued on a blockchain. These are securities because the underlying instrument is one. The blockchain is a distribution medium, not a classification-altering feature.
Crypto-asset-related securities — tokens whose value depends on a team's essential managerial efforts and which were sold with an expectation of profit in a common enterprise. These satisfy all four Howey prongs. The full regulatory apparatus applies: registration, periodic disclosure, insider-trading prohibition, supervisory oversight.
2. Separation — the release's most consequential innovation (§IV.B, pp. 28–34)
This is arguably the single most important legal concept in the entire document.
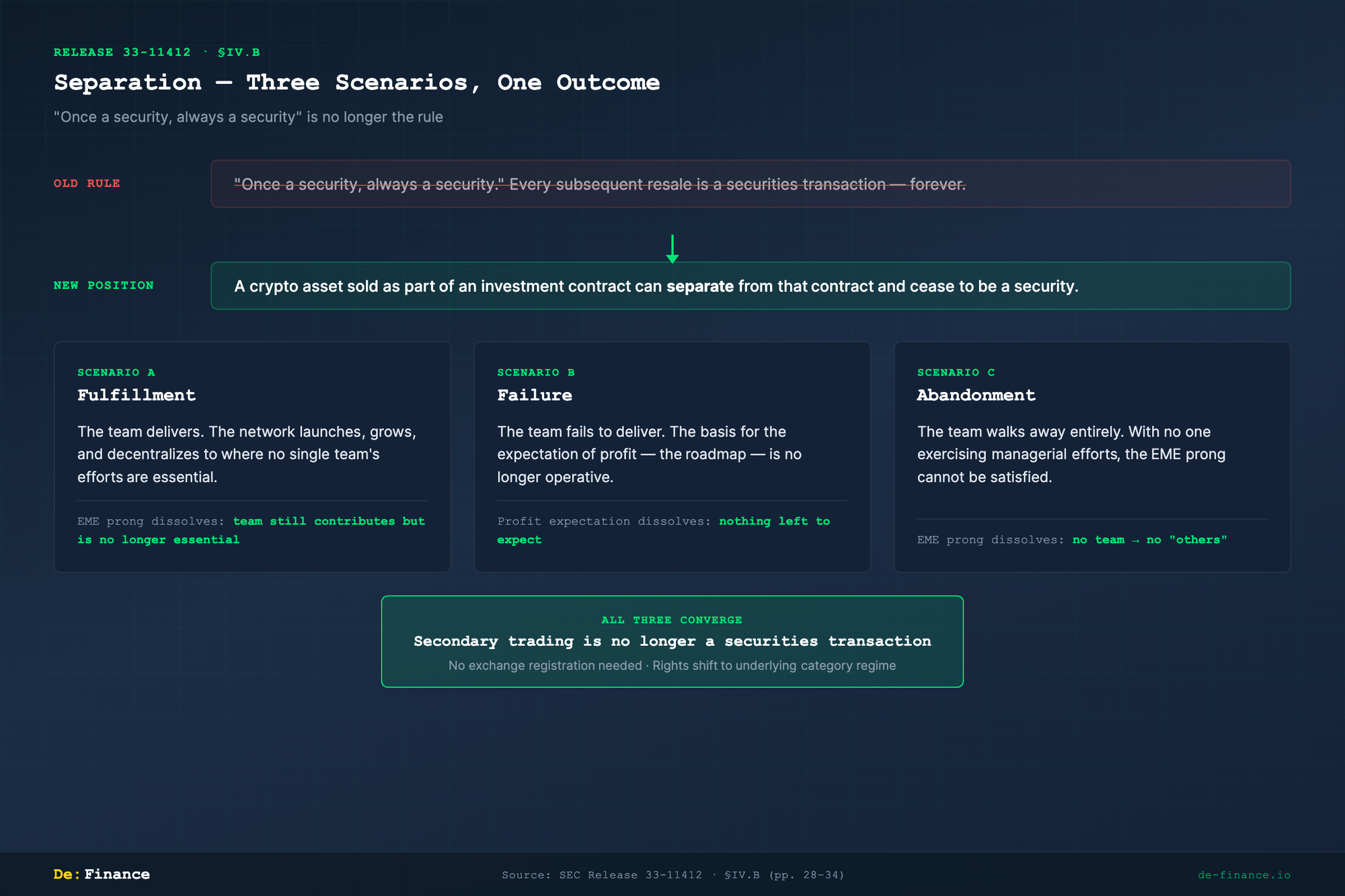
The old assumption: "Once a security, always a security." If a token was sold as part of an investment contract, every subsequent resale was also a securities transaction — forever.
The new position: A crypto asset sold as part of an investment contract can, over time, separate from that contract and cease to be a security.
The release identifies three scenarios that trigger separation:
Scenario A — Fulfillment (pp. 29–31)
The team delivers on its promises. The network launches, grows, and decentralizes to a point where no single team's efforts are essential — they may still contribute, but the ecosystem no longer depends on them for its economic viability.
At that point, the investment contract dissolves. The underlying crypto asset — which was always a commodity or collectible by nature — reverts to its non-security classification. Secondary-market trading is no longer a securities transaction.
This is the formalization of Bill Hinman's 2018 "sufficiently decentralized" concept. What was a speech is now Commission-level interpretive guidance.
Scenario B — Failure (pp. 31–33)
The team fails to deliver. The project does not reach its goals. The investment contract unwinds because the basis for the expectation of profit — the team's roadmap, its promises, its managerial trajectory — is no longer operative. If there is nothing left to expect, there is no "expectation of profit."
Scenario C — Abandonment (pp. 33–34)
The team walks away entirely. With no team exercising managerial efforts, the "efforts of others" prong can no longer be satisfied. The asset may still have value (market-driven, speculative), but it is not securities-law value.
What separation means in practice
In all three scenarios:
- Secondary-market trading of the token is no longer a securities transaction
- Exchanges that list the token after separation do not need to register as securities exchanges for purposes of that token
- The token holder's rights and obligations shift from the securities-law regime to whichever regime applies to the asset's underlying category (commodity regulation, consumer protection, or none)
3. Technical rulings — where law meets protocol design (§V–VII, pp. 34–63)Redeemable at par on demand No profit expectation Marketed without expectation of return
If a stablecoin's issuer advertises yield or investment return, the carve-out does not apply and the token may be analyzed as a security.
1-E. Digital Securities (§III.E, pp. 23–24)
The residual category. Two sub-types:
Tokenized securities — traditional financial instruments (bonds, equity, fund interests) issued on a blockchain. These are securities because the underlying instrument is one. The blockchain is a distribution medium, not a classification-altering feature.
Crypto-asset-related securities — tokens whose value depends on a team's essential managerial efforts and which were sold with an expectation of profit in a common enterprise. These satisfy all four Howey prongs. The full regulatory apparatus applies: registration, periodic disclosure, insider-trading prohibition, supervisory oversight.
2. Separation — the release's most consequential innovation (§IV.B, pp. 28–34)
This is arguably the single most important legal concept in the entire document.
The old assumption: "Once a security, always a security." If a token was sold as part of an investment contract, every subsequent resale was also a securities transaction — forever.
The new position: A crypto asset sold as part of an investment contract can, over time, separate from that contract and cease to be a security.
The release identifies three scenarios that trigger separation:
Scenario A — Fulfillment (pp. 29–31)
The team delivers on its promises. The network launches, grows, and decentralizes to a point where no single team's efforts are essential — they may still contribute, but the ecosystem no longer depends on them for its economic viability.
At that point, the investment contract dissolves. The underlying crypto asset — which was always a commodity or collectible by nature — reverts to its non-security classification. Secondary-market trading is no longer a securities transaction.
This is the formalization of Bill Hinman's 2018 "sufficiently decentralized" concept. What was a speech is now Commission-level interpretive guidance.
Scenario B — Failure (pp. 31–33)
The team fails to deliver. The project does not reach its goals. The investment contract unwinds because the basis for the expectation of profit — the team's roadmap, its promises, its managerial trajectory — is no longer operative. If there is nothing left to expect, there is no "expectation of profit."
Scenario C — Abandonment (pp. 33–34)
The team walks away entirely. With no team exercising managerial efforts, the "efforts of others" prong can no longer be satisfied. The asset may still have value (market-driven, speculative), but it is not securities-law value.
What separation means in practice
In all three scenarios:
- Secondary-market trading of the token is no longer a securities transaction
- Exchanges that list the token after separation do not need to register as securities exchanges for purposes of that token
- The token holder's rights and obligations shift from the securities-law regime to whichever regime applies to the asset's underlying category (commodity regulation, consumer protection, or none)
3. Technical rulings — where law meets protocol design (§V–VII, pp. 34–63)
Sections V through VII of the release address specific crypto-native activities. These are the rulings where legal interpretation meets protocol-level engineering, and they will matter most to builders and exchange operators.
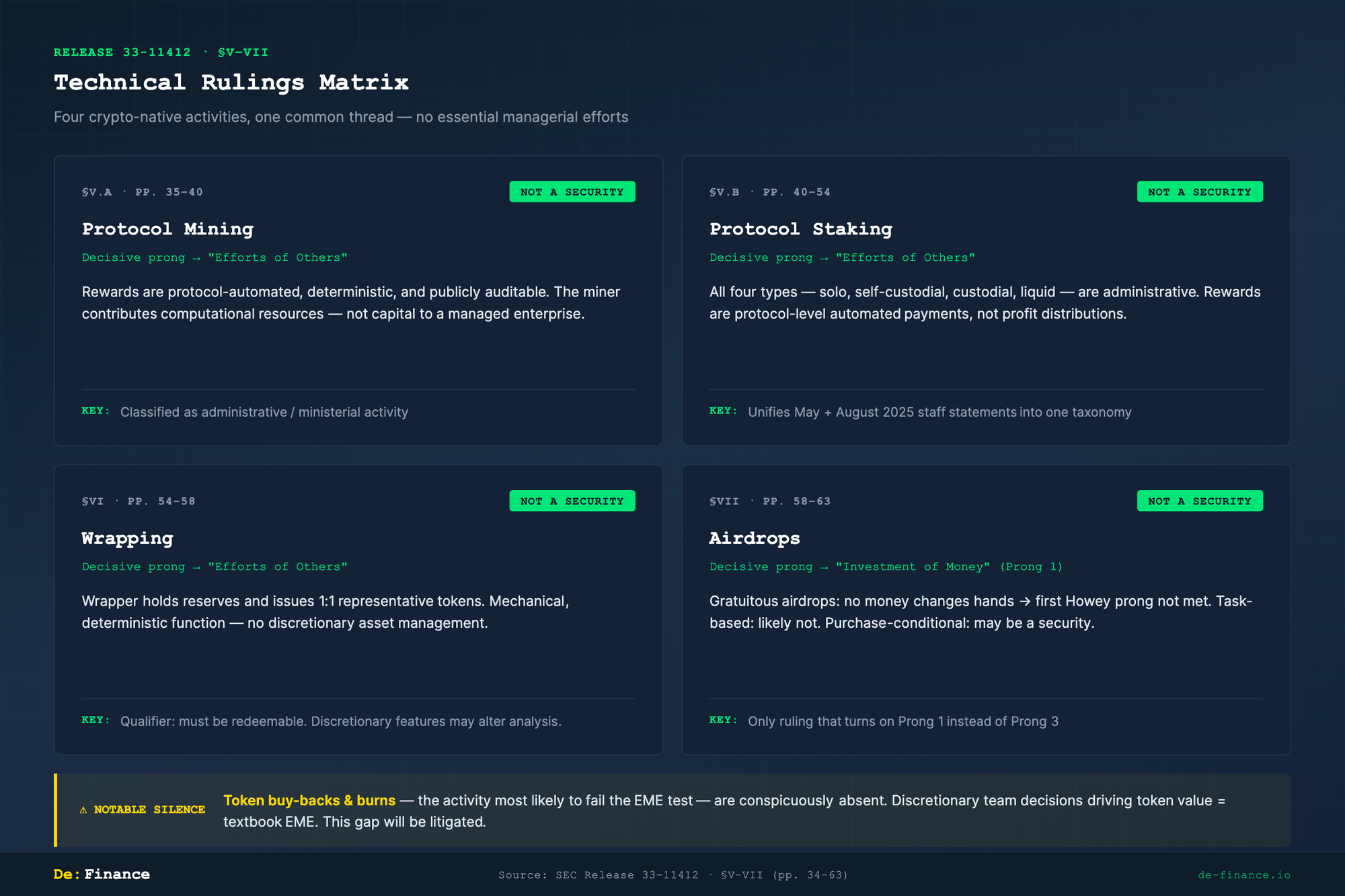
3-A. Protocol Mining (§V.A, pp. 35–40)
Why this ruling matters. Mining sits at the intersection of the third Howey prong — "efforts of others" — and the threshold question of whether protocol-level automated rewards can ever constitute a return from someone else's managerial effort. If mining rewards were securities, every PoW miner would be an unregistered securities recipient, and every mining pool a potential investment scheme. The stakes are structural: the ruling determines whether the consensus layer itself — the mechanism that keeps blockchains alive — operates inside or outside the securities perimeter.
Ruling: Proof-of-Work mining is not a securities transaction.
The reasoning follows the essential-managerial-efforts line directly:
| Factor | Analysis |
|---|---|
| Who decides the reward? | The protocol's consensus algorithm, not a team's discretionary choice |
| Is the reward predictable? | Yes — block reward schedules are public, deterministic, and auditable by anyone |
| Does the miner depend on a team's decisions? | No — the miner contributes computational resources and receives protocol-automated compensation |
| Information asymmetry? | None — every parameter is visible on-chain |
Mining is classified as an administrative or ministerial activity. The miner is performing work for the network, not investing in a common enterprise managed by others.
3-B. Protocol Staking (§V.B, pp. 40–54)
Why this ruling matters. Staking was the most contested question in crypto-securities law before this release — because two distinct analytical paths led to different reasons for the same conclusion. One path focused on the "efforts of others" prong: are protocol-automated rewards the product of someone else's essential managerial effort? The other focused on "expectation of profits": does a staker expect profit, or merely receive a mechanical reward for infrastructure participation? The release resolves this by collapsing all four staking types into a single administrative-activity framework.
Ruling: All four types of staking are not securities transactions.
This is the section that consolidates the May 2025 (protocol staking) and August 2025 (liquid staking) staff statements into a unified taxonomy:
| Staking type | Description | Securities status |
|---|---|---|
| Self (Solo) Staking | Validator runs own node, stakes own tokens directly to the protocol | Not a security |
| Self-Custodial Staking | Token holder delegates staking power to a validator but retains custody of tokens | Not a security |
| Custodial Arrangement | Token holder transfers tokens to a staking service provider who stakes on their behalf | Not a security |
| Liquid Staking | Token holder deposits tokens into a liquid staking protocol and receives a derivative token (e.g., stETH) representing the staked position | Not a security |
The common thread: in every case, rewards are protocol-level automated payments, not distributions of profit from a managed enterprise. The validator or staking service may take a fee, but the fee is for a service (infrastructure operation), not for managerial effort that drives the token's value.
The liquid staking distinction is particularly significant. Before the August 2025 staff statement, there was genuine uncertainty about whether liquid staking tokens (stETH, rETH, etc.) constituted securities — because the holder receives a new token from a protocol that pools assets. The release resolves this: the liquid staking protocol is performing an administrative function (aggregating stake, distributing rewards), not exercising essential managerial efforts over the staked assets' economic future.
Slashing. The release addresses slashing risk — the possibility that a validator loses staked tokens due to protocol violations — and concludes that slashing is a protocol-enforced penalty, not a loss attributable to managerial failure. It does not change the non-security characterization.
3-C. Wrapping (§VI, pp. 54–58)
Why this ruling matters. Wrapping is the plumbing that connects isolated blockchains into a single liquidity surface. If wrapped tokens were securities, every cross-chain bridge would be an unregistered securities issuer, and every DeFi protocol that accepts wBTC or wETH would be handling securities. The ruling matters because it draws the line between mechanical asset representation (non-security) and discretionary asset management (potential security) — the same essential-managerial-efforts line that runs through the entire release, applied here to the specific act of holding reserves and minting representative tokens. The key variable is whether the wrapping protocol exercises judgment over the deposited assets or merely performs a deterministic 1:1 function.
Ruling: The issuance and sale of redeemable wrapped tokens is not a securities transaction.
Wrapping is the process of depositing a token on one chain and receiving a representative token on another (e.g., depositing BTC and receiving wBTC on Ethereum). The release analyzes the mechanics:
| Factor | Analysis |
|---|---|
| What does the wrapper do? | Holds the original asset in reserve and issues a 1:1 representative token |
| Is there an expectation of profit from wrapping? | No — the wrapped token is designed to maintain parity with the underlying asset, not to generate return |
| Essential managerial efforts? | No — the wrapping protocol executes a mechanical, deterministic function |
| Information asymmetry? | Minimal — reserve ratios, redemption mechanisms, and smart contract logic are publicly auditable |
The key qualifier: redeemable. The wrapped token must be exchangeable back to the underlying asset. If a wrapping protocol introduces discretionary features — variable fees, reserve reallocation, yield generation from deposited assets — the analysis could change.
3-D. Airdrops (§VII, pp. 58–63)
Why this ruling matters. Airdrops test the first Howey prong — "investment of money" — rather than the third or fourth. This makes the analysis structurally different from mining, staking, and wrapping, all of which turn on the "efforts of others" question. The logic is straightforward — if no money changes hands, no investment contract can exist. But the boundary cases matter enormously for token distribution strategy: task-based airdrops (requiring social media posts or referrals) and purchase-conditional airdrops (receive token B when you buy token A) push the analysis toward ambiguity, because the "consideration" question re-enters through the back door.
Ruling: Gratuitous airdrops are not investment contracts.
The reasoning is elemental: the Howey test requires an investment of money. If a token is distributed for free — no purchase, no swap, no consideration of any kind — the first prong is not satisfied and the inquiry ends.
| Airdrop type | Securities analysis |
|---|---|
| Pure gratuitous (free, no conditions beyond wallet eligibility) | Not a security — no investment of money |
| Task-based (requires social media posts, referrals, etc.) | Likely not a security — tasks are promotional, not investment of money |
| Purchase-conditional (receive token B when you buy token A) | May be a security — the purchase of token A could constitute the investment of money for the combined package |
The release is cautious on the boundary: "The analysis depends on the totality of the circumstances, including whether the airdrop is part of a broader scheme to distribute tokens in connection with a fundraising effort."
4. The gap the release chose not to fill: buy-back and burn
Why this gap matters. The release cleared mining, staking, wrapping, and airdrops by running each through the same essential-managerial-efforts test. Buy-backs are the activity that would most likely fail that test — and the release chose not to run it. The "efforts of others" prong is the direct collision point: unlike protocol-automated mining rewards or deterministic wrapping, a buy-back is a team's discretionary decision about timing, scale, and price — the textbook definition of essential managerial effort. The "expectation of profits" prong is also in tension: once a buy-back program is announced, token holders can reasonably expect that the team's purchases and burns will reduce supply and support price — an expectation that looks like Howey's "expectation of profits derived from the efforts of others." And the traditional-securities analogy is the strongest here: stock buy-backs are regulated under SEC Rule 10b-18 precisely because they carry the same manipulation risks. Addressing token buy-backs would force the Commission to confront the uncomfortable parallel between a mechanism it just declined to regulate and one it has regulated for decades.
One notable absence runs through the entire document. The release addresses mining, staking (all four types), wrapping, and airdrops — but says nothing about token buy-backs and burns.
This is not an oversight. Buy-backs sit at the uncomfortable intersection of the release's own categories:
| Buy-back characteristic | Why it is problematic |
|---|---|
| Discretionary | The team decides when, how much, and at what price to buy — a textbook essential managerial effort |
| Supply-affecting | Burning purchased tokens directly reduces circulating supply, mechanically supporting price |
| Asymmetrically informed | The team knows the timing, scale, and funding source of the buy-back before the market does |
| Analogous to stock repurchases | In traditional securities markets, stock buy-backs are heavily regulated under SEC Rule 10b-18 precisely because of their potential for manipulation |
By the release's own logic — does a team's discretionary decision-making drive the asset's value? — a token buy-back program looks like an essential managerial effort. A team that uses treasury funds to buy its own token on the open market and burn it is exercising exactly the kind of insider-informed, value-affecting discretion that the release uses to distinguish securities from non-securities.
The silence is almost certainly deliberate. Addressing buy-backs would require the Commission to either (a) classify a widely used DeFi mechanism as a securities-law event, creating immediate compliance burdens for hundreds of projects, or (b) carve out an exception that would be difficult to reconcile with Rule 10b-18's treatment of the identical activity in traditional markets.
This gap will be litigated. Any enforcement action targeting a token project's buy-back program will need to confront the asymmetry: the release explicitly cleared mining, staking, wrapping, and airdrops, but left buy-backs in legal limbo. Defense counsel will argue selective treatment; the SEC will argue that silence is not approval. The outcome will shape the next iteration of the framework.
5. Where each 2025 staff statement sits
Throughout 2025, the SEC's Division of Corporation Finance published a sequence of staff statements. Release 33-11412 elevates and consolidates them into a common analytical frame — the essential-managerial-efforts test. Here is the mapping:
| Staff Statement (2025) | Release section | Classification | Rationale |
|---|---|---|---|
| Meme Coins (Feb) | §III.B Digital Collectibles | Non-security | No essential managerial efforts; price driven by sentiment, not a team's decisions |
| PoW Mining (Mar) | §V Mining and Staking | Non-security | Ministerial; protocol-automated rewards |
| Certain Stablecoins (Apr) | §III.D Stablecoins | Non-security | GENIUS Act carve-out; no profit expectation |
| Protocol Staking (May) | §V Mining and Staking | Non-security | Ministerial; all four staking types covered |
| Liquid Staking (Aug) | §V Mining and Staking | Non-security | Ministerial; included in staking taxonomy |
The staff said "this is not a security." The Commission now says "here is why it is not a security, and the reason is the same in every case: no essential managerial efforts."
What comes next
Posts 01a, 01b, and 01c have covered the what — how the release lands in Korea (01a), the legal test it is built on (01b), and the framework it creates (01c).
Post 02, "From Enforcement to Framework," turns to the how: a nine-year arc from the DAO Report (2017) through the enforcement peak (2022–2023) to the rulemaking pivot (2025–2026). The history matters because the release is not a blank-slate design — it is a negotiated settlement between an agency that spent a decade enforcing, an industry that spent a decade resisting, and a Congress that decided, in the end, to legislate. Reading the release without that context is like reading a peace treaty without knowing the war.